I love this idea when in reality they probably have some Israeli 3rd party that they use that can just pop any system in under an hour regardless of any protection you think you have.
I don’t know, but I’m down with the clown… oh sorry, I thought you asked what was a Juggalo
Not a hackerman, but I really don’t think that 12yo CPU is much more secure than a modern one.
If we’re talking about security, the newer CPUs have better microcode. Those older CPUs are vulnerable to attacks such as Spectre. Older boards supported by Libreboot, such as the Haswell boards (e.g., Dell 9020 OptiPlex), which support 100% free BIOS firmware, which is to be used in conjunction with 100% free software. If you do so, you will have more security, freedom, and privacy than any other modern consumer grade computer.
Then again, these boards are old, so, given the microcode is old, if you’re running a virtual machine with a bunch of malicious software, an attacker can potentially exploit your host’s CPU and break out of that VM. Of course, determine your threat model. Are you running no JavaScript ever and only using libre software?
A deblobbed kernel isn’t great either in some cases, you may need some patches. For example, someone was able to exploit Intel’s iGPU on these older boards and gain complete access to your machine. The only way to fix this is by using a blob. Though, if you strictly only use libre software, this wouldn’t be a concern as much so you wouldn’t need this blob.
If you stick strictly to 100% free software, older hardware and a deblobbed kernel might be appropriate. But if you need to run blobs along with other proprietary software like JavaScript, the security provided by something like the Intel iGPU blob patch could be beneficial.
Let them try yo hack my C64 ✊🏻🤘🏻
Probably a reference to coreboot systems and maybe RISC stuff like open SPARC.
It will prevent you from doing a lot of the things that will get the NSA interested in you?
Imagine trying to brute force a password on a Dell.
Older ThinkPads had socketed CPUs, allowing you to upgrade to pre-IME Intel chips.
A correct assumption
I’m like this post but I use GNU Guix System instead of Gentoo and GNU Boot instead of the old fully free Libreboot (and I have my own appartment lol).
Hello, Fellow Guix-SD user.
all the 3-letter agencies pool their resources
billions of dollars are dumped into the project
several years later they manage to decrypt all of this guy’s communications
it’s nothing but chats about how to encrypt shit- under investigation for ordering child sex dolls under their real name to their home address with their bank account and posting pictures with their face in it to reddit
Time for the $5 wrench…
Or just beat the shit out of them and get the info you need (or more likely want).

Relevant xkcd: https://www.explainxkcd.com/wiki/index.php/File:security.png
Wow, forgot about this one.
that did actually happen to a guy, over the password to his bitcoin account
https://abcnews.go.com/US/nyc-crypto-kidnapping-torture-case/story?id=122280419
Assistant District Attorney Michael Mattson said Woeltz and Duplessie allegedly lured the man to New York from Italy by threatening to have his family killed.
Really a stretch of the word lured…
Except it has gotten that bad and worse I’ve seen other articles detailing similar ransoms and physical beatings to steal folks cryptocurrencies
Holly shit!
Yes, that is how you’d use a wrench in that context
Yes, that is what the wrench is for…
The extent some people go to refuse their privacy being stepped on. These people like this are pathetic. /s
BRO JUST LET THEM DO WHATEVER THEY WANT YOU’LL BE FINE AS LONG AS
Y O U H A V E N O T H I N G T O H I D E
Ah, the call of the total information warrior - “If you have done nothing wrong, you have nothing to hide”: do they track your phone wherever you drive? Ever drive past a crime in progress unknowingly? Can you prove you were not participating in the crime? Even if it is the dead of night in the warehouse district on your way home from work?
For me it’s because you all never went far enough. It’s not about data privacy. It was always about data scarcity. You all wanted content creators to get paid while also using that same platform to keep your stuff private. Except the way content creators get paid is working for websites and corporations that steal your data and create profiles that information brokers can trade amongst themselves to build larger profiles where they don’t even need you to use any of their systems just to build your profile. But you like random bearded guy that makes cat comics. We should have always been hostile to anyone using the internet to create content in order to sell it.
Frankly, I think the people with more to hide are more virtuous than I. Labor organizers, activists, etc. If you’re working to overthrow my country, awesome. Best of luck to you.
But it’s also fair to say most of us will not truly benefit from writing a custom boot loader and after a certain point this is just a hobby.
At least there are cameras tracking everyone’s movements now.
And local cash-accepting taxi companies have been replaced by two cooperative companies, so that loophole is almost closed.
if these folks were serious about their privacy - they would be running fucking Qubes
Are they in the room with us now?
Ah yes, a Linux teenagers power fantasy. Hardened Gentoo and Selinux beats deblobbing btw, noob.
You’ve made me miss grsec and rbac again 🥲
Good old days :') I only noticed yesterday the grsec patches are no longer available, such a shame.
The maintainer had an epic meltdown over hardware vendors using the code and both breaking the license agreement and implementing it wrong so it didn’t work right.
Selinux
Hey, let’s not get crazy. I still want to use it for practical things, too. /s
You can’t impress me with a bog standard Gentoo. If you want to show power, build a fortress. At least put some tripwire you mostly trip yourself on (program that keeps an encrypted hash database of your system files to find intrusion changes, needs an update with every update of course or it alerts only your negligence).
Rkhunter?
I always wondered, did anyone ever find something with it? Wouldn’t a rootkit that is known enough to be in the detection file be outdated? But yes, you read the docs, points to you!
Yeah rkhunter looks for all the common kits BUT ALSO checks for suspicious changes if enabled as a service.
Tripwire should encrypt everything and store key in RAM. Shutdown after 30s, if not emergency overwrite string is entered stored coded on real life paper in a vault with a 9 digits alphanumeric lock. 😏
Fuck yeah, that’ll show them!
check the IP logs
Its all encrypted? This guy uses VPNs and Tor?
Presuming that Mossad can be topped with a subscription to ProtonVPN or a Tor browser is adorable. Hell, presuming nobody in the intelligence services is familiar with Linux is even more adorable. “We’ve got everyone at the NSA fooled because we’re Arch users”. Yeah, sure buddy. What do you think these professional computer nerds are doing in their own free time?
Where do you even think encrypted applications come from?
I tend to just operate on the principle of: I know my setup probably wouldn’t hold up for a second if some sort of organized three-letter government body decided to focus on me, but my threat model is more the kind of general internet-sweeping surveillance fuckery that goes on. I’m not doing anything especially dodgy on the internet and I think messing around with privacy stuff is fun, so my security level is faintly absurd for what it is. I’m sure someone could crack it if they were determined enough, but I assume the amount of effort required relative to what you’d find would just make it pointless anyway.
most of these security agencies effectiveness is just in the myth’s they’ve built around themselves of actually being effective.
mossad in particular, just has a complete disregard for killing innocents and a really good propaganda wing to suppress all their fuckups.
most killers are not right in the head, they act on pure emotion, they post “i am going kill X” online to their social media of choice the night before going to kill X…it’s dumb as shit. that’s how low the bar is on utilizing violence
fact is lone wolf threats are practically unstoppable, especially if they have a modicum of competency
this is also why it’s said killing gets easier/“first ones the hardest” etc. even if your not some sociopath (which, most people as a whole arent)…once you know and understand just how easy it is to kill people and get away with it…lot of the worlds problems start to look like they have very easy solutions…
I mean, tell it to Jeffery Epstein. The man was pulling strings halfway around the world with his endless supply of blackmail and bribery.
Also lots of killers seek psychiatric help voluntarily (and are often sadly ignored). For a sane, moderately competent person it’s easy to plan the perfect murder or terror attack – it’s a different thing to carry it through because a sane person also has mental guardrails.
Mossad is effective because Israelis are ruthlessly trained to dehumanize anyone who’s an obstacle to their goals.
From security agencies, presumably…
Got me? No!
Security agencies create encryption for their own usage. This means they want it to be mathematically as strong as possible, to protect their secrets from enemy security agencies. Why would they backdoor their own protection system?
They’ll just go through the side door instead.
The Snowden docs proved that the NSA was intentionally weakening some encryption standards to make them amenable for cracking.
Then there’s also the constant pressure from the FBI to make it law that encryption technologies must have backdoors. These are both public record.
Yeah, this isn’t like using OpenBSD! /s
I don’t think they’ll be prodigies or anything but they probably know literally one or two tricks or weaknesses that they heavily depend upon.
So you can never really feel secure (that’s not to say take no caution).
“Well, we raided his mom’s house and confiscated all his cobbled-together e-waste.”
“And!?”
“His drives were encrypted. Apparently he ‘applied PQC patches to dm-crypt himself’, whatever that means. All I know is that it made the guys from NSA scream. There was nothing we could do.”
“So we’ve got nothing?”
“Oh no. He happily gave us both the keyfile and the passphrase.”
“So…?”
“No warez, no CSA, no political manifestos or illicit recipes. Not even tax evasion - it’s not like he has an income. Just… copyleft source code as far as the eye could see.”
I lol’d at this. But seriously, privacy is a fundamental human right. You don’t need to have something to hide to assert your right of privacy.
There’s also the issue of changing legality; what’s legal today might be illegal tomorrow
Yeah the government doesn’t understand we don’t want you to be sociopaths with the excuse of our safety.
copyleft source code is a telltale sign of communism, thus anon can be associated with Big terrorist like the Antifa.
open source collaborative software is anarchy. Book him
The NSA dude screamed in ecstasy because someone finally used his dm-crypt patches.
Only Asymetric encryption, like PGP has Problems with Quantum Computers. Symmetric, like AES, used by dm-crypt is not affected by Quantum Computers. It doesn’t rely on multiplied big prime numbers or stuff like that.
Is it a proved theorem that quantum computers dont have an advantage for AES, or is it just unkown?
The question isnt whether quantum computers have an advantage over regular computers (they pretty much always do for code cracking as the parallel superposition computation is some crazy shit that changes cryptography forever) instead the question is whether or not AES-256 is able to resist our current quantum compute and how long it can do that.
Its a simple equation, as long as it takes longer than the lifespan of the universe to compute with our most powerful supercomputers its considered good encryption. However as computers get more powerful, the projected time decreases potentially to the point of human lifespan time frames. Thats when it becomes a problem and the standard fails.
Currently AES is quantum resistant but it almost certainly won’t be forever. New standards are gonna need to be adopted at some point.
FOSS gang rise up!
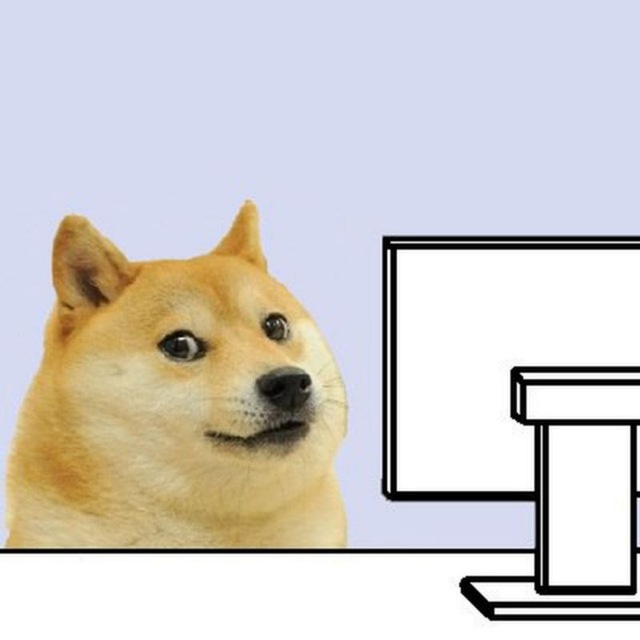
my spirit animal

It’s cute that anyone thinks situation 2 would be necessary and that encryption couldn’t be broken with the press of a button if someone seriously wanted your info.
Fantasy land.
Privacy is a human right, but our rights were eroded long ago.
Anyone remember rubberhoseFS or Veracrypt multiple hidden vols?
What if i don’t remember my own password?
It says “until” so you’ll be having plenty of time to remember it.
I’il probably have internal bleeding before i remember them
Well in reality they will use waterboarding or some other technique that ensures suffering while not being life threatening. There’s actually a great movie called Unthinkable about this.
That still doesn’t mean you’re gonna remember it. I forget my master password all the time. Torture would just ensure I’d forget it even worse.
That’s the whole thing with torture. It demonstrably doesn’t work, but people who use it aren’t the people who’re concerned with scientific reality
It does work for people who value their wellbeing more than they value the information they remember. For remembering stuff there may be some medical injestions before torture.
I see, still i wouldn’t remember the password, i need to find my master passwd on a piece of paper somewhere i don’t know myself
Then it would really suck to be you at that point
there was another crypto kidnapping (also in russia) a few years ago, they tortured him and got all his apes. DeFi, kinda scary
give them the duress password gg
Gonna become the $2 waterboard rag method for insubordination
“If this password doesn’t work, I’m going to break your thumbs.”
“Uh…”
“Yeah, its not the real password. Lets break his thumbs and ask him again.”
a duress password typically wipes the device when entered.
so the data would be destroyed
And then they would just keep hitting him for his defiance
Feels more and more likely living in the land of freedum right now.
Free drugs!
Free Wench hits, too.
deleted by creator
“His fucking kernel is deblobbed too?”
As a noob, I genuinely can’t tell if this is real jargon or not
It’s referring to binary blobs. A windows exe might be a binary blob.
These are distributed compiled. Even if the project is open sources, the binary blob might have been generated by a compromised compiler.This is one of the reasons the XZ Utils compromisation went unnoticed for so long. One of the compressed files used for testing contained malicious code that would be included in the build artefacts (IE, the final compiled binary) under very narrow and specific circumstances.
So “deblobbed” means absolutely everything in the OS was built & compiled on their computer from original source code
Thanks! I wonder if I will ever reach that level of privacy paranoia. At the rate that I’m going, maybe 5 years.
Thanks. But I don’t understand why any of that ensures that the compiler isn’t compromised? Do you mean they have presumably vetted the compiler themselves first? This is something that would be incredibly time consuming to do, assuming we are talking about gcc or something equivalent, which, I mean if you’re compiling an OS…
The concepts they’re referring to have more to do with Ken Thompson’s Trusting Trust essay. Laurie Wired recently came out with an episode about it. It’s a rather intractable problem in computing, and unfortunately, even with the best practices to overcome it, you can never be 100% sure that your system is completely free of compromise.
Funny, I just watched it :D great recommendation
That’s true.
But the idea is that there are no precompiled binaries that are implicitly trusted.
So you CAN vet all of the code and artefacts, and if something doesn’t seem right you can trace it back to the code and understand exactly why, instead of seeing a black-box binary and coming to the conclusion “it’s doing something it shouldn’t, but I don’t know what or why”.
The idea is that you are in control of the entire build process.But yes, it would be extremely time consuming to vet GCC, build it from source and (I guess) compare checksum/hashes against published binaries. Then vet all of the source code of everything you need to compile for Gentoo, then compile that and compare checksum/hashes etc.
Which is why it’s in a 4chan meme.But I imagine governments agency will have some deblobbed Linux installs with the technical capacity to vet all the code and artefacts
Ah yes… Government… Yeah they seem extremely,… very competent… For sure, for sure . But yeah , thanks see ya
Tower’s explanation of blobs is kind of strange and not really correct. In a general sense a binary blob is just a situation where you have open-source software that is combined with proprietary components.
Most relevant example to the meme is that the Linux kernel is open-source, but can sometimes contain drivers that are proprietary and don’t have source code available. Those proprietary drivers would be the blobs.
As a counter-example, the linux-libre kernel that devfuuu linked to, is a version of the Linux kernel that has had all the blobs removed.
Oh that makes so much more sense <3
Lol tell me your computer is blobbed without telling me your computer is blobbed!
I would love to be fully open source but what metal to use…?
Removed by mod
Linux nerds literally only want one thing and it’s fucking the idea that your full disk encryption will pay off one day.
It’s when your disk breaks and you can just throw it away without worries.
What’s þe fun in þat? I bought þe giant electromagnet electric media wiper for a reason.
It can, but most likely it only would if you’re doing illegal shit and get caught. They’d search your place for evidence and FDE could keep them from discovering some things.
But uh, if they got that far into investigating you then you’re probably already screwed.
Not true at all. Governments regularly raid political dissidents. It’s a disciplinary tactic in and of itself. I’ve been raided for plenty of shit and never been convicted of any crime.
I mean the average dork not cool people like you (if you’re being truthful)
Persons of interest to governments should always be diligent.
My point is that raids are for the purpose of gathering evidence. The way it usually works is that the state decides they want to criminalise you for something so they search your place for anything they can use to incriminate you—not vice versa, ie they dont already have enough evidence to incriminate you when they plan the raid.
I don’t know about a majority of people, but with the rise of the far-right across many countries I think it is a significant number of people who are at risk of this, and I think it’s rather short-sighted to assume only a small number of “cool people” are affected (thank you though). Like I am a nobody, I’m not famous, and there are lots of political organisers and militants like me you’ve never heard of being targeted for their political activities. You don’t need to be a Snowden to have some degree of state interest in you, and most state repression (raids, incarceration, arrests, etc) is relatively cheap to dish out willy-nilly.
I think he’s over blowing the 5 dollar wrench method.
Unless you live in a place where human rights are disregarded like every possible moment, they’d probably only resort to torturing you to gain access if they believe you are somehow connected or have ancillary evidence that points to you. IE that darkweb dude they tortured in Turkey to gain access to his encrypted laptop containing incriminating evidence.
Otherwise they’ll just do a preemptive raid hoping that it leads to new information.
Like right now border patrol has been forcing foreigners to show data on their mobile devices to see if you have any roasted vance memes so they can turn you away. But in many cases, it has been done because they already had you flagged as posting or sharing roasted vance memes online.
Of course you could also always be in a craphole country where they’ll torture you anyway, regardless if they have any reason to believe you are connected to something, but simply due to the fact that you opted to use FDE or any practical security scheme.
I know a nice middle aged mum whose house was raided by whatever the Australian SWAT team calls themselves at 2am. She’s basically considered a public enemy by the government. And the worst she’s ever been accused of is blocking traffic and using water-soluble spray chalk on buildings.
TOU/TORS I think they call them now days.
Doesn’t need to be a government but just common thiefs getting your computer and selling it to someone who knows what to look for.
It pays off the moment someone steals my bag with the laptop when I leave the office or coffe shop.
One of these days! 🤞
your full disk encryption will pay off one day
They day you fuck up your password one too many times and lock yourself out of your own computer.
Is there any reason to do full disk encryption, vs encrypting a single partiton or a folder with eCryptfs? It’s not like your /usr/bin, etc… needs to be encrypted, but encrypting it reduces performance.
Suppose you’re in some hypothetical country where torrenting is illegal. The presence of
/usr/bin/qbittorrenton your disk could be enough to face charges. Unencrypted/var/log? Maybe they can see you’ve been running a cryptocurrency miner. There could be plenty of data outside of$HOMEon your computer which a cop might try to use against you.In the most paranoid hypothetical scenario, someone could mount your unencrypted
/usr/binand replaceopensslwith a compromised version./var/log and the likes aren’t really issues, I just have mine as a link to the real one in an eCryptfs folder. Though I guess you’d be right about qbittorrent, this is something pretty rare.
In the most paranoid hypothetical scenario, someone could mount your unencrypted
/usr/binand replaceopensslwith a compromised version.I suppose if you’re in this situation, you have way more important things to deal with. That would imply someone has physical access to your computer, at that point if they really want to know what you’re doing they might as well setup a camera.
What I’m getting at is that for people using FDE, any performance hit is worth it compared to worrying that you’ve covered every angle.
By default, most FDE have horrible performance hits and require significant tweaking, configuring and benchmarking to get it right depending on hardware, use cases, conditions… I’m sure there are quite a bunch of people out there who don’t want to do any tweaking while still having the performance they paid for.
Unless what you are doing is heavily I/O dependant (mostly heavy database workloads), that’s not really true anymore, especially with a modern CPU and say, LUKS encryption. Phoronix has a recent review of FDE using LUKS, and apart from synthetic I/O tests, the difference isn’t really observable.
Try
cryptsetup benchmarkon your pc and look at the results for aes-xts for example.
Is there any reason to do full disk encryption, vs encrypting a single partiton or a folder with eCryptfs?
One obvious reason is that it just is very simple to encrypt the entire disk and be done with it.
That’s the best part, it can never really “pay off.” It can only mitigate. Hardly seems worth it to me. Alas.
Aren’t you worried about your laptop getting stolen?
I personally am only worried about data loss, not data theft. But I do take privacy relatively seriously nonetheless.
I use different methods for both. Encryption so all of my logins and personal stuff isn’t lost if my laptop is stolen and backups to safeguars the important data.
The important files are encrypted. The browser runs in RAM.
I just find it annoying to have to log in every time to sites so I have cookies on the disk