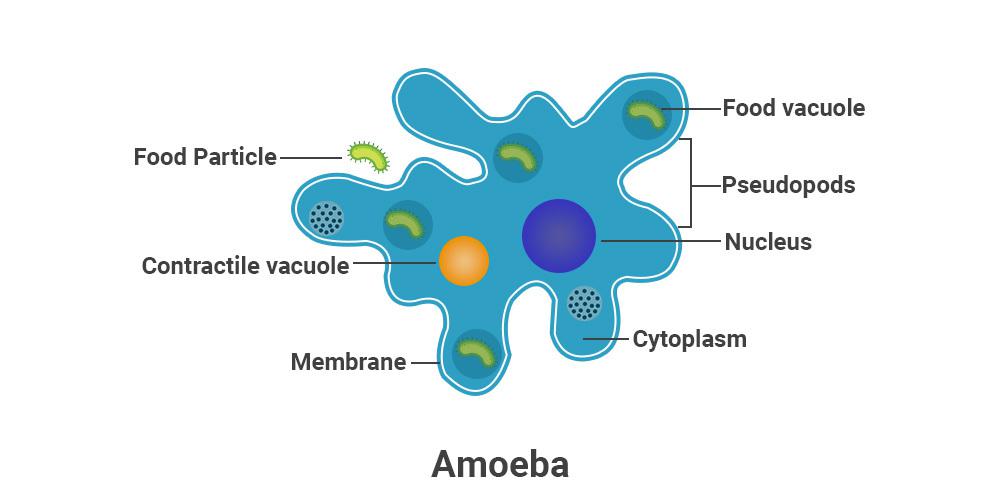
Avid Amoeba
- 49 Posts
- 2.41K Comments

 2·4 days ago
2·4 days agoThere’s the midterms. But yeah. :D

 13·4 days ago
13·4 days agoAlso the last time I checked, his base isn’t quite hot on sending more money or getting involved militarily in Ukraine. He’d get popular with Democrats. But they won’t thank him for it at the voting booth. 😅

 44·4 days ago
44·4 days agoIt must. Too many things are going badly at home, so they gotta put some darker-skinned people murder on the TV.

 1·4 days ago
1·4 days agoThat’s odd because the clients are just web apps I think. That should work without crashing on a stable OS. I use them on Android mobile and Android TV with extensive subtitle usage and haven’t seen instability.
A funny thing I noticed is that the client distributed in F-Droid is extremely old even though it says it’s updated recently.

 111·5 days ago
111·5 days agoI switched from a heavily used Plex server with about 10 users to Jellyfin with the samw usage patterns abour half a year ago. So far it’s been pretty smooth sailing. A better world is possible!

 6·5 days ago
6·5 days agoA cushy job in the private sector.

 1·5 days ago
1·5 days agoHm, I thought Chromecast needs HTTPS and internet-visible endpoint.

 1·6 days ago
1·6 days agoOh? I haven’t upgraded yet. 😄

 12·6 days ago
12·6 days agoThat’s how it works with Tailscale as well. Tailscale creates Wireguard tunnels underneath between the different devices. There’s also an open-source self-hostable Tailscale control plane.

 7·6 days ago
7·6 days agoI do use both a reverse proxy and Tailscale. All services are proxied. All services except for Jellyfin are accessed only via Tailscale. Jellyfin is publicly available. I’ve obscured it a bit by setting up long, randomly generated DNS name. The proxy would only forward traffic to Jellyfin if the request comes from that exact DNS name. Bots would have to know this name for the proxy to entertain their attempts at all. Then every user has long, randomly-generated password. I prefer to only use it behind Tailscale but some of my family needs direct access. Also Chromecast.

 17·6 days ago
17·6 days ago
The latest number is 88.7.

 4·6 days ago
4·6 days agoI do. No issues.

 901·6 days ago
901·6 days agoSwitched to Jellyfin after more than a decade with Plex. Prettey… prettey… pretty good.
That’s the issue. It’s why I’ve learned that when I can afford it and I reasonably believe this firm or project should exist, and it has a decent chance not to fall flat, I end up buying in. It’s literally upfront investment in the thing. I’m still salty for not backing the Ubuntu Phone back in 2012 or so. I looked at it as another phone compared to what’s available on the market and how the price stacks up for the features. That’s very much the wrong way to do it. A part of the value it provides is the existence of the project and the labour dedicated to it. In the case of the new Pebble, I’m backing it despite Eric, and because it’s fully open source and that’s something I want to exist. A fully open alternative in the sea of proprietary wearable crap.
Same guy. This time the whole thing is open source though, even the hardware. So that’s insurance for what it’s worth.
This is not the final design, it might gain a connector in the final. It might not. But even if it doesn’t, splicing the wires shouldn’t be too difficult for most who’d dare open their watch. I’m pretty confident I can do it.

 7·7 days ago
7·7 days agoLike, comment and subscribe. Make this one famous.
True, but it shouldn’t be a huge deal to clean them up once every few years.













This is cool but for self-hosting you probably want a more robust monitoring system capable of alerting at all times. Prometheus is what I use. It also gathers data over time and can monitor many machines.